For CISOs, security leaders, and compliance teams
NIS2 Directive
Compliance Made
Manageable
Turn NIS2 obligations into assigned controls, linked evidence, and board-visible progress across risk management, incidents, supplier governance, and oversight duties.
What is the NIS2 Directive?
The NIS2 Directive (Directive (EU) 2022/2555) is the EU's updated cybersecurity legislation, replacing the original NIS Directive from 2016. It establishes a high common level of cybersecurity across the European Union, significantly expanding the scope from roughly 10,000 entities under NIS1 to over 160,000 under NIS2.
NIS2 introduces stricter requirements for risk management, incident reporting, supply chain security, and governance, including personal accountability for management bodies. Member States were required to transpose the directive into national law by October 2024.
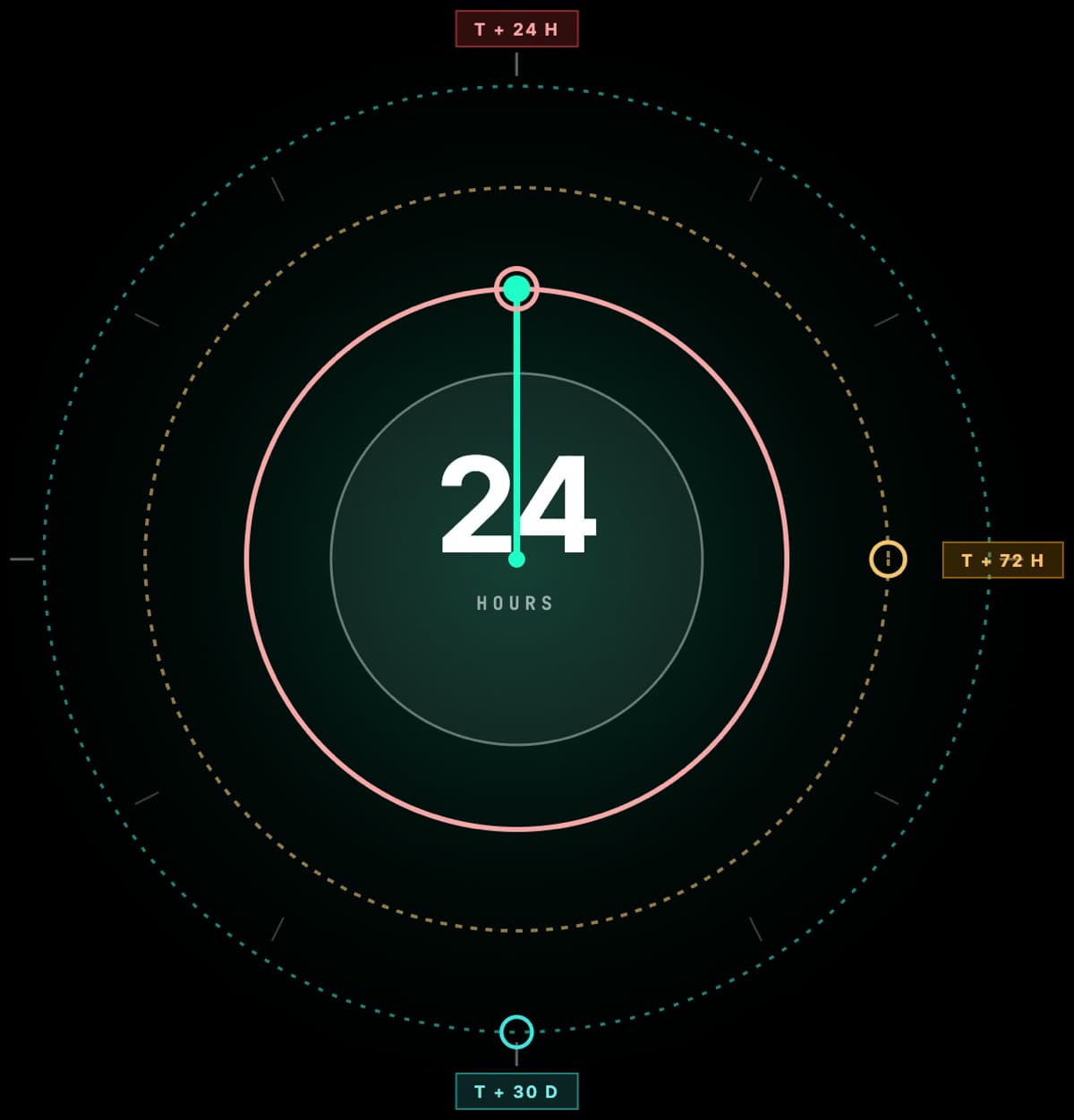
Timeline and Compliance Milestones
The NIS2 Directive was adopted in December 2022 with a 21-month transposition period. The 17 October 2024 transposition deadline has passed, while national implementation and enforcement remain uneven across Member States. Use this timeline to benchmark urgency and sequence readiness activities.
European Commission proposes the NIS2 Directive to replace the original NIS Directive from 2016
Directive adopted and published in the Official Journal; 21-month transposition period begins
Article 41(1) transposition deadline (17 October); NIS2 applies from 18 October 2024, and the original NIS Directive is repealed from the same date under Article 44
Article 3(3) deadline for Member States to compile and maintain lists of essential entities, important entities, and entities providing domain name registration services
European Commission issues reasoned opinions to 19 Member States for not notifying full transposition after the October 2024 deadline
First Commission review of NIS2 functioning and effectiveness (Article 40)
European Commission proposes the NIS2 Directive to replace the original NIS Directive from 2016
Directive adopted and published in the Official Journal; 21-month transposition period begins
Article 41(1) transposition deadline (17 October); NIS2 applies from 18 October 2024, and the original NIS Directive is repealed from the same date under Article 44
Article 3(3) deadline for Member States to compile and maintain lists of essential entities, important entities, and entities providing domain name registration services
European Commission issues reasoned opinions to 19 Member States for not notifying full transposition after the October 2024 deadline
First Commission review of NIS2 functioning and effectiveness (Article 40)
European Commission proposes the NIS2 Directive to replace the original NIS Directive from 2016
Directive adopted and published in the Official Journal; 21-month transposition period begins
Article 41(1) transposition deadline (17 October); NIS2 applies from 18 October 2024, and the original NIS Directive is repealed from the same date under Article 44
Article 3(3) deadline for Member States to compile and maintain lists of essential entities, important entities, and entities providing domain name registration services
European Commission issues reasoned opinions to 19 Member States for not notifying full transposition after the October 2024 deadline
First Commission review of NIS2 functioning and effectiveness (Article 40)
Who is Subject to NIS2?
NIS2 uses a size-cap rule combined with sector classification for most entities. Certain digital and ICT service providers can also be in scope even when not established in the EU.
The Size-Cap Rule (Article 2)
Organizations in covered sectors are in scope if they meet either threshold:
Size doesn't matter for some. Article 2(2) lists exceptions where entities are in scope regardless of size, including DNS service providers, TLD name registries, trust service providers, and certain public electronic communications entities.
Annex I (Sectors of High Criticality)
Mostly essential entities. Stricter supervision and minimum maximum fine of at least €10M / 2%.
- Energy
- Transport
- Banking
- Financial market infrastructure
- Health
- Drinking water
- Waste water
- Digital infrastructure
- ICT service management (B2B)
- Public administration
- Space
Annex II (Other Critical Sectors)
Mostly important entities. Reactive supervision and minimum maximum fine of at least €7M / 1.4%.
- Postal and courier services
- Waste management
- Chemicals
- Food production & distribution
- Manufacturing (medical devices, electronics, machinery, motor vehicles)
- Digital providers (marketplaces, search engines, social networks)
- Research organisations
Article 26 Jurisdiction for Certain Non-EU Providers
Article 26(1)(b) applies to specific non-EU digital and ICT providers offering services in the EU: DNS service providers, TLD name registries, domain name registration service providers, cloud computing service providers, data centre service providers, content delivery network providers, managed service providers, managed security service providers, and providers of online marketplaces, online search engines, and social networking services. These entities must designate a representative in one Member State where services are offered.
Example: A US-based cloud provider serving EU customers can fall within Article 26 jurisdiction even without an EU office. It must appoint an EU representative and comply with NIS2 obligations that apply to its service category.
10 Mandatory Cybersecurity Measures
Article 21(2) of NIS2 prescribes 10 minimum cybersecurity risk-management measures that both Essential and Important entities must implement.
Risk Analysis & Security Policies
Establish and maintain comprehensive risk analysis and information system security policies.
Incident Handling
Prevention, detection, analysis, containment, response, and recovery from security incidents.
Business Continuity
Backup management, disaster recovery, and crisis management procedures.
Supply Chain Security
Assess and manage security risks from direct suppliers and service providers.
Secure Development & Vulnerability Handling
Security in network and information systems acquisition, development, and maintenance, including vulnerability handling and disclosure where appropriate.
Effectiveness Assessment
Policies and procedures to regularly assess the effectiveness of cybersecurity measures.
Cyber Hygiene & Training
Basic cyber hygiene practices and cybersecurity training across staff. Article 20(2) makes specific cybersecurity training mandatory for management bodies on top.
Cryptography & Encryption
Policies governing the use of cryptography and encryption where applicable.
Access Control & HR Security
Human resources security, access control policies, and comprehensive asset management.
Multi-Factor Authentication
MFA or continuous authentication, secured communications, and emergency systems.
Incident Reporting Timeline
NIS2 introduces strict incident reporting obligations under Article 23. Organizations must report significant incidents in four stages.
Early Warning
Article 23(4)(a). Submit an early warning to the CSIRT or competent authority, indicating whether the incident is suspected of being caused by unlawful or malicious acts or could have a cross-border impact.
Incident Notification
Article 23(4)(b). Provide an initial assessment including severity, impact, and indicators of compromise; updates the early warning.
Intermediate Report
Article 23(4)(c). On request from the CSIRT or competent authority, provide relevant status updates while the incident is still being handled.
Final Report
Article 23(4)(d). Within one month after the 72-hour notification, deliver root cause analysis, mitigation measures applied, and any cross-border impact. Article 23(4)(e) sets a progress-report rule for ongoing incidents.
Penalties for Non-Compliance
Article 34 sets minimum maximum administrative fines: member states must allow at least the figures below, and national law may set higher caps.
Essential Entities
Article 34(4): minimum maximum fine. Essential entities mostly come from the Annex I sectors of high criticality (energy, transport, banking, health, digital infrastructure) and are subject to proactive supervision.
Important Entities
Article 34(5): minimum maximum fine. Important entities mostly come from the Annex II other-critical sectors (manufacturing, food, chemicals, postal services, digital providers, research) and are subject to reactive supervision.
Under Article 20, management bodies must approve and oversee the Article 21(2) cybersecurity risk-management measures and may be held liable for failures. For essential entities, supervisory authorities can also exercise the exceptional Article 32(5) power to request a temporary prohibition of CEO or legal-representative-level duties when measures remain ineffective despite enforcement.
How Modulos Helps with NIS2 Compliance
Modulos gives compliance and security teams one workflow for requirements, controls, evidence, reviews, and exports. This helps you move faster from legal text to operational execution with clearer ownership and stronger auditability.
Book a NIS2 DemoTranslate NIS2 obligations into structured requirements and mapped controls so teams know exactly what needs to be done and by whom.
FAQ about NIS2
The NIS2 Directive (Directive (EU) 2022/2555) is the EU’s updated cybersecurity legislation, replacing the original NIS Directive of 2016. It expands the scope of regulated entities, raises baseline cybersecurity requirements, and tightens incident reporting obligations. EU member states had to transpose NIS2 into national law by 17 October 2024.
NIS2 stands for the second Network and Information Security Directive (Directive (EU) 2022/2555). It is the EU’s second-generation cybersecurity framework for essential and important entities, replacing Directive (EU) 2016/1148. NIS2 raises baseline cybersecurity requirements, expands sectoral scope, and tightens incident reporting across 18 sectors.
The NIS2 Directive entered into force on 16 January 2023. EU member states were required to transpose it into national law by 17 October 2024 under Article 41, with NIS2 applicable and the original NIS Directive (2016/1148) repealed from 18 October 2024 under Article 44. On 7 May 2025 the European Commission issued reasoned opinions to 19 Member States for non-full transposition. Verify the country-specific implementation status before relying on national readiness.
Yes, for entities in scope. NIS2 is binding EU law transposed into national legislation across the member states. In-scope essential and important entities must implement the Article 21(2) cybersecurity risk-management measures and the Article 23 incident reporting obligations. Non-compliance exposes entities to Article 34 administrative fines, with additional enforcement powers for essential entities under Article 32.
NIS2 covers two annexes. Annex I lists sectors of high criticality (energy, transport, banking, financial market infrastructure, health, drinking water, waste water, digital infrastructure, ICT service management (B2B), public administration, space). Annex II lists other critical sectors (postal and courier services, waste management, chemicals, food, manufacturing, digital providers, research). Article 3 then sets the classification rule for essential vs important status, based on sector, entity size, special provider categories, and Member State CER identification.
Medium and large entities (≥ 50 employees or > €10M annual turnover or balance sheet) operating in the 18 sectors listed in Annexes I and II. Article 2(2) also brings certain entities into scope regardless of size, including DNS service providers, TLD name registries, trust service providers, and specific public electronic communications providers. Non-EU digital and ICT providers in the Article 26(1)(b) categories that offer those services in the EU also fall under Article 26 jurisdiction in addition to the Article 2 scope rules.
The UK has not adopted NIS2; it follows the UK NIS Regulations 2018, with a UK Cyber Security and Resilience Bill introduced to Parliament in November 2025 as the planned NIS2-equivalent reform. UK companies that fall within the Article 26(1)(b) provider categories (DNS, TLD, domain registration, cloud, data centre, CDN, managed services, managed security services, online marketplaces, search engines, social platforms) and offer those services in the EU may fall under NIS2 jurisdiction for those services. The UK domestic regime and EU NIS2 obligations can apply simultaneously.
Article 21(2) sets ten cybersecurity risk-management measures: (a) risk-analysis and information-system security policies; (b) incident handling; (c) business continuity, backup, and crisis management; (d) supply-chain security; (e) security in network and information-system acquisition, development, and maintenance with vulnerability handling; (f) effectiveness assessment of risk-management measures; (g) basic cyber hygiene and cybersecurity training; (h) cryptography policies; (i) human-resources security, access control, and asset management; (j) multi-factor authentication and secured communications. Article 23 adds incident-reporting obligations on top.
Article 23(4) sets four stages for significant incidents: (a) an early warning to the CSIRT or competent authority within 24 hours of becoming aware; (b) an incident notification within 72 hours of awareness, with an initial severity and impact assessment; (c) an intermediate report on request; (d) a final report within one month of the incident notification under (b). For ongoing incidents, a progress report is also required.
Under Article 34, member states must allow administrative fines of at least €10 million or 2% of total worldwide annual turnover (whichever is higher) for essential entities, and at least €7 million or 1.4% for important entities. National caps may be set higher. Article 20 makes management bodies responsible for approving and overseeing the Article 21(2) measures and exposes them to individual liability. For essential entities, supervisory authorities can also exercise the exceptional Article 32(5) power to request a temporary prohibition of CEO or legal-representative duties when measures remain ineffective.
Most NIS2 Article 21(2) risk-management measures map directly to ISO/IEC 27001 controls. Holding ISO/IEC 27001 certification does not satisfy NIS2 by itself: there is no formal presumption of conformity in the directive. It does provide a defensible operational baseline that significantly reduces NIS2 implementation effort, which is why most mature security programs operate ISO/IEC 27001 inside their NIS2 compliance approach.
Modulos automates the governance, risk, and compliance workflow that NIS2 Article 21(2) expects: risk-management policy documentation, incident-response evidence, supply-chain risk records, and audit trails for security controls. Controls map across NIS2, ISO/IEC 27001, ISO/IEC 42001, the EU AI Act, and SOC 2 simultaneously, so one evidence pipeline serves multiple frameworks.
How NIS2 fits with other frameworks
Most security teams run NIS2 alongside other regimes rather than instead of them.
Article 21(2) of NIS2 maps directly onto the controls in ISO/IEC 27001 for information security; ISO/IEC 42001 supports the AI-management portion indirectly. There is no formal presumption of conformity, but most mature security programs run NIS2 inside an ISO/IEC 27001 management system.
For financial sector entities, Article 4 of NIS2 disapplies equivalent NIS2 risk-management and incident-reporting provisions where the Digital Operational Resilience Act (DORA) covers the same matter. NIS2 governance and supply-chain provisions that are not covered by DORA may still apply alongside.
For AI systems specifically, the EU AI Act and GDPR sit alongside NIS2 with overlapping risk-management and supply-chain expectations. Risk operating models such as the NIST AI RMF support the Article 21(2)(a) risk-analysis duty without substituting for it.
For US-attestation work, SOC 2 control sets often share evidence with NIS2 cybersecurity-measure controls, especially around access, change, and incident management.
Need a Practical NIS2 Rollout Plan?
In a live walkthrough, see how to structure obligations, assign owners, and prepare audit-ready evidence without duplicating work.